Disconnected Edge: Separated Perimeter Sections
In the ever-evolving landscape of cybersecurity, the classic notion of a single, fortified castle wall protecting your digital kingdom is not just outdated—it’s dangerously insufficient. Today’s threats are sophisticated, persistent, and capable of exploiting the slightest weakness in a monolithic defense. This reality has given rise to a more nuanced and resilient strategy: the Disconnected Edge, achieved through intentionally Separated Perimeter Sections. Far from being a sign of fragmentation, this architectural approach represents a mature, layered defense model that limits breach impact, controls lateral movement, and aligns security with business logic. This blog post will delve into what this concept means, why it’s critical for modern organizations, and how to implement it effectively.
From Moat to Islands: Redefining the Network Perimeter
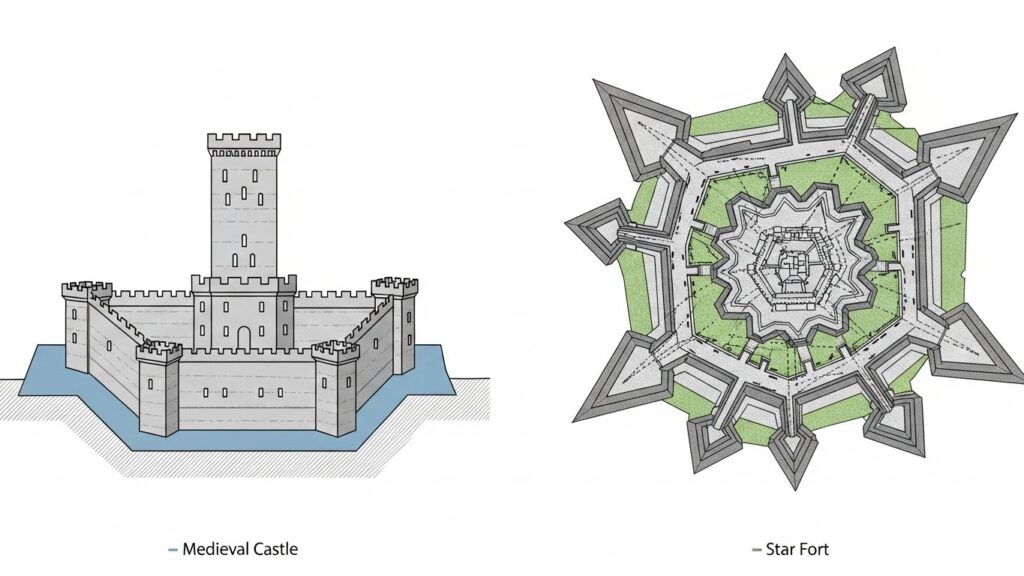
For decades, network security followed the “castle-and-moat” model. A strong firewall at the network edge acted as the moat, keeping threats out, while everything inside was implicitly trusted. This model assumed a clear inside (trusted) and outside (untrusted). However, the explosion of cloud services, remote work, IoT devices, and sophisticated attacks like phishing and supply chain compromises has utterly blurred that line. The “moat” is now full of authorized but potentially risky connections, and once an attacker is inside, they often face minimal obstacles moving laterally to critical assets.
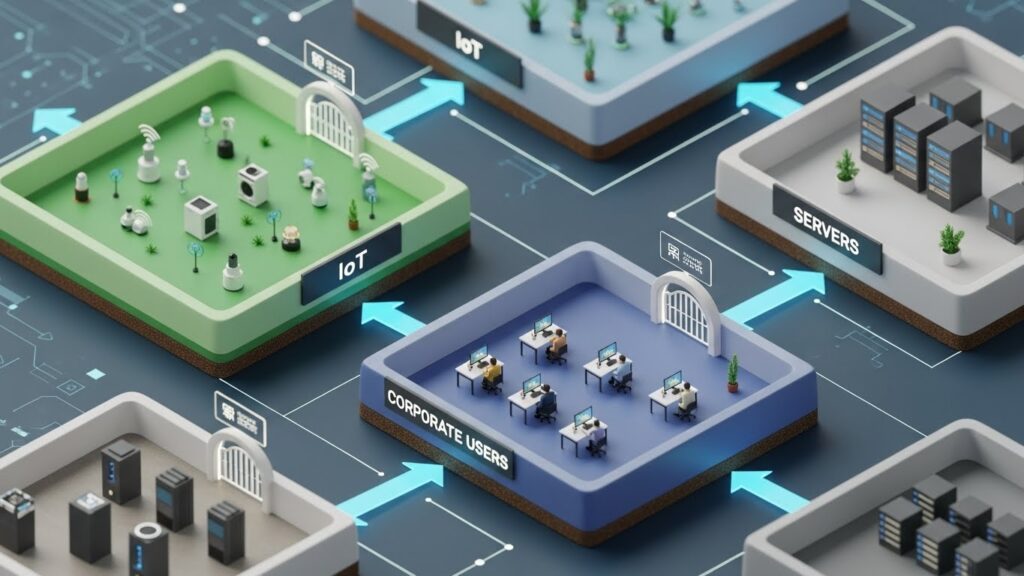
The Disconnected Edge philosophy abandons the idea of one contiguous perimeter. Instead, it advocates for creating multiple, smaller perimeters around logical groupings of assets—these are your Separated Perimeter Sections. Think of it as building a series of specialized islands instead of one massive continent. Each island (e.g., the finance department network, the IoT sensor network, the developer environment) has its own defined shoreline and controlled ports for communication. A breach on one island does not automatically grant access to the others.
The Core Principles: Segmentation, Least Privilege, and Micro-Perimeters
Implementing a Disconnected Edge rests on three foundational security principles, applied with granular intent.
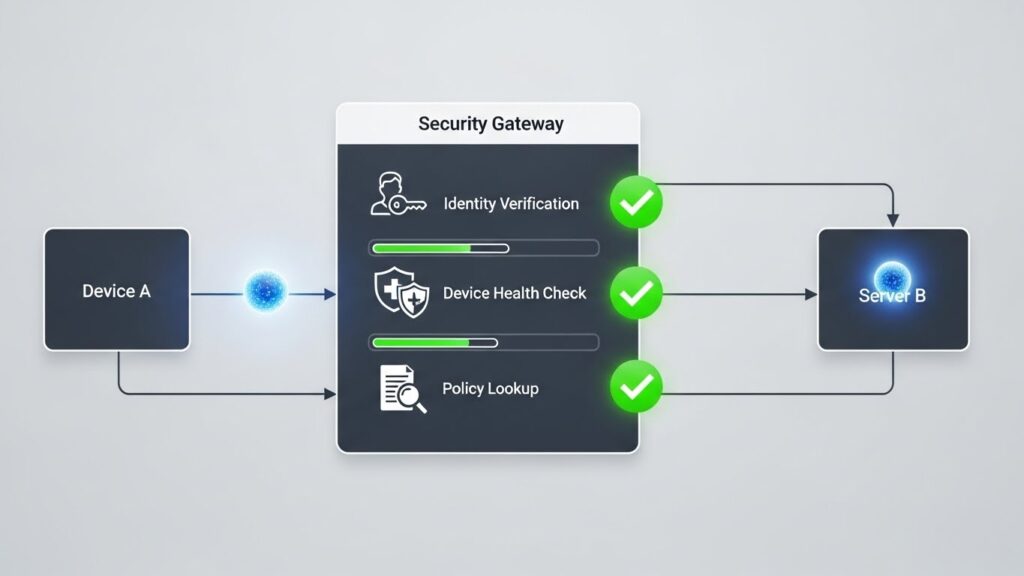
1. Granular Network Segmentation: This is the technical mechanism that creates the separated sections. It goes beyond simple VLANs to enforce policy-based segmentation, often using firewalls (both physical and virtual), Software-Defined Perimeter (SDP) technology, or advanced network access control (NAC). Traffic between segments is denied by default and only permitted through explicit, justified rules.
2. The Principle of Least Privilege: Applied at the network level, this principle dictates that a system or user should only have access to the network resources and communications paths absolutely necessary for its function. Your HVAC controller has zero reason to initiate a connection to your financial database server. Separated perimeter sections enforce this logically.
3. Micro-Perimeters (or Zero Trust Edge): The ultimate evolution is to define the perimeter around individual workloads or data sets. This is the essence of Zero Trust architecture, where trust is never assumed based on location. Each application or data store becomes its own “section,” with identity and context-aware policies governing access, effectively creating a disconnected edge at every critical point.
Tangible Benefits: Why Go Through the Trouble?
Adopting this model requires planning and effort, but the security and operational payoffs are substantial.
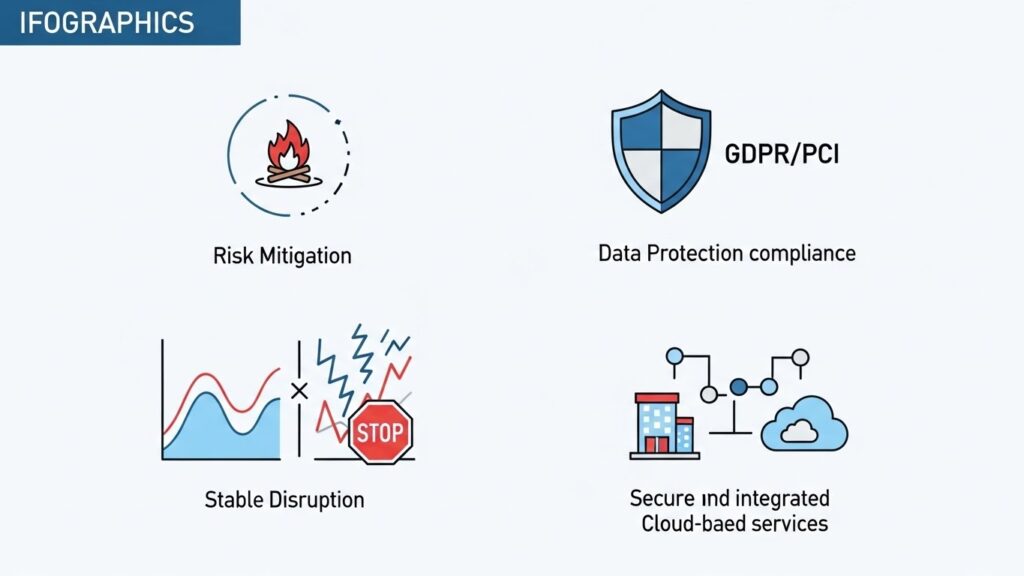
Containment of Breaches: This is the most significant benefit. If ransomware infects a marketing department workstation, strong segmentation can prevent it from encrypting files on the R&D or production servers. The attacker’s lateral movement is stifled, dramatically reducing the blast radius and cost of the incident.
Improved Regulatory Compliance: Many regulations (like PCI DSS, GDPR, HIPAA) mandate the protection of specific data types. Separated perimeter sections make it far easier to isolate cardholder data, personal health information, or other sensitive datasets, simplifying audit trails and demonstrating due care.
Operational Stability and Performance: By isolating network traffic, you prevent issues in one section (e.g., a misconfigured device causing a broadcast storm) from bringing down the entire network. This also allows for tailored performance and monitoring policies for each section.
Adaptability to Hybrid Environments: This strategy is cloud-agnostic. You can define perimeter sections that span on-premises data centers and public cloud VPCs/VNets, creating a consistent security posture across your hybrid infrastructure.
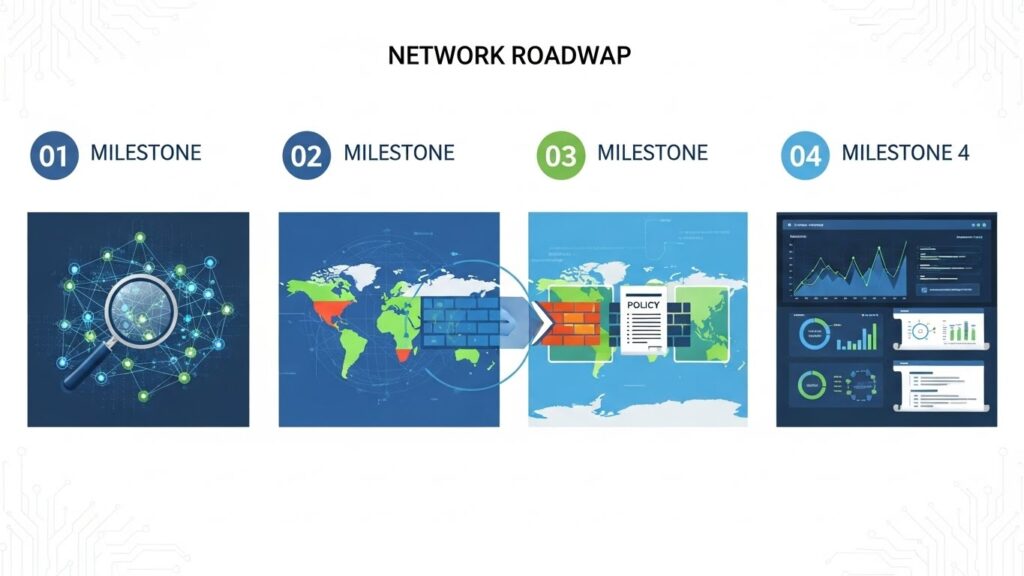
Implementation Roadmap: Building Your Sections
Moving to a disconnected edge architecture is a journey, not a flip-of-a-switch event. Follow these steps to build a robust, separated perimeter.
Step 1: Discovery and Classification: You cannot protect what you don’t know. Use asset discovery tools to map your entire network—devices, applications, data flows. Classify assets based on sensitivity, function, and compliance requirements. This forms the blueprint for your sections.
Step 2: Define Security Zones: Group assets into logical zones. Common starting points include: Corporate Users, Guest WiFi, IoT/OT Devices, PCI Cardholder Data Environment, Critical Servers, Developer/Test Environments. Each zone will become a separated perimeter section.
Step 3: Establish Chokepoints and Policy: Identify the necessary communication paths between zones. Implement next-generation firewalls, internal gateways, or micro-segmentation software at these chokepoints. Craft explicit “allow” policies based on the least privilege principle. Document every rule with a business justification.
Step 4: Deploy and Monitor Iteratively: Roll out segmentation in phases, starting with the most critical or risky zones (like your cardholder data). Use a monitoring and logging system to watch inter-zone traffic, validate policies, and catch any misconfigurations before a full rollout.
Challenges and Considerations
While powerful, this approach is not without its challenges. Awareness and planning are key to overcoming them.
Management Complexity: More sections mean more policies to manage. Investing in a centralized security management platform that provides a single pane of glass for policy across on-prem and cloud firewalls is crucial.
Potential for Business Disruption: Overly aggressive or incorrect segmentation can break legitimate application workflows. This is why the discovery and mapping phase is critical, and why changes must be tested in a staging environment first.
Performance Overhead: Every policy check introduces a minuscule latency. For most traffic, this is negligible, but for extremely high-performance computing or low-latency trading environments, careful design is needed to balance security and speed.
Cultural Shift: This model requires IT, security, and application teams to collaborate more closely. Developers may need to understand network policies when designing applications. Overcoming the “it’s always worked this way” mentality is often the biggest hurdle.
The Future-Proof Architecture
The trend towards distributed work, ubiquitous cloud adoption, and hyper-connected operations is irreversible. In this environment, the rigid, single-edge perimeter is a liability. The strategic adoption of a Disconnected Edge through Separated Perimeter Sections is not merely a tactical security upgrade; it is a fundamental architectural shift that aligns defense with modern reality.
It moves security from being a static, border-guarding function to a dynamic, adaptive, and integral part of the network fabric itself. By compartmentalizing risk, you build inherent resilience. When one section faces a storm, the entire fleet doesn’t sink. Start your segmentation journey today—map your assets, define your zones, and begin building the isolated, intelligent islands that will form the robust archipelago of your future-proof network.